Penetration testing, commonly referred to as pen testing, is a critical exercise in cybersecurity, where experts simulate cyberattacks to identify and exploit vulnerabilities in computer systems. This process is akin to a bank hiring someone to test their security by attempting a break-in; it's a proactive measure to strengthen defences against real threats.
Pen testing approaches
Penetration testing, a critical component of cybersecurity defence strategies, employs various approaches to identify vulnerabilities. Each method offers unique perspectives, mimicking different attacker scenarios to ensure comprehensive system evaluation. From simulating uninformed external attacks to in-depth internal analyses, these approaches provide valuable insights into system robustness and security preparedness. Understanding these methodologies is key to appreciating the depth and complexity of penetration testing, ultimately contributing to stronger, more resilient cyber defences. Let's delve into each approach to uncover how they individually contribute to a holistic security assessment.
1. External/Black box testing
In this approach, testers have little to no information about the internal workings of the target system. It simulates an external hacker's perspective, focusing on exploiting externally visible weaknesses like those in public-facing websites and servers. Black box testing effectively assesses the robustness of the system's external defences against uninformed attackers.
2. Internal/White box testing
This is the direct opposite of black box testing. Here, testers are provided complete information about the system, including access to source code, network layouts, and credentials. This approach allows for a comprehensive examination from an insider's point of view, identifying vulnerabilities that might be missed by external testing. It's particularly useful for uncovering deep-rooted issues in complex systems.
3. Blind testing
In blind testing, the penetration tester is given only the name of the target organisation. This approach mimics a real-world attack scenario where the attacker has minimal information. It provides insights into how an actual attack unfolds and tests the organisation's detection and response capabilities.
4. Double-blind testing
Even more realistic than blind testing, double-blind tests involve situations where both the testers and the organisation's security team are unaware of the impending test. This method tests the security monitoring and incident response in real-time conditions, offering a true test of how well an organisation can detect and respond to an unanticipated attack.
5. Targeted testing
Also known as 'lights-on' testing, here, the tester and the organisation's security team work together throughout the test. It's a collaborative approach that provides the security team with immediate feedback from the hacker's perspective. This type of testing is particularly beneficial for educational purposes and for improving the understanding and readiness of the security team.
Exploring the types of pentests
Penetration testing is not a one-size-fits-all solution. It encompasses a variety of types, each designed to tackle specific aspects of an organisation's cybersecurity infrastructure. From scrutinising network services to evaluating the resilience of web applications, and from examining the human element in security to testing cutting-edge IoT devices, each type of penetration testing plays a pivotal role. Understanding these diverse methodologies is crucial for a comprehensive security assessment, ensuring that every potential vulnerability is accounted for and mitigated. Let's explore these types in detail to understand their unique objectives and importance in fortifying cybersecurity defences.
1. Network services penetration testing
This type focuses on identifying and exploiting vulnerabilities in an organisation's network infrastructure. It involves scrutinising both external and internal network defences, including firewalls, network devices, and servers. The goal is to uncover weaknesses that could be exploited by attackers, ranging from unauthorised access to data breaches. Network service tests are crucial in ensuring that the infrastructure backbone of an organisation is secure against potential threats.
2. Web application penetration testing
This type targets web-based applications, seeking out vulnerabilities that could be exploited by attackers. Testers simulate attacks on web applications to identify security gaps like unsanitised inputs vulnerable to code injection attacks. This testing is vital for safeguarding online platforms, particularly as web applications become increasingly integral to business operations.
3. Client-side penetration testing
This involves testing the security of client-side applications—software that users interact with directly. Testers look for vulnerabilities that could be exploited through user interfaces or client-side scripts. This type of testing is essential for ensuring that end-user applications are secure and cannot be manipulated to compromise the user's system.
4. Wireless network pen testing
This type focuses on the security of wireless networks, such as Wi-Fi. Testers attempt to exploit vulnerabilities related to wireless network protocols and encryption methods. With the increasing use of wireless networks in corporate environments, ensuring their security is critical to prevent unauthorised access and data breaches.
5. Social engineering pen testing
Unlike other types which focus on technical vulnerabilities, social engineering tests the human element of security. Testers use tactics like phishing to assess how employees respond to attempts at manipulation or deception. This type of testing is crucial in a comprehensive security strategy as human error or manipulation often leads to breaches.
6. Red team attack simulation
This is a comprehensive approach where testers, or the 'Red Team', simulate real-world attackers to test an organisation's defences. The objective is to evaluate how well an organisation can detect and respond to sophisticated attacks. It's a more aggressive form of testing that assesses the overall strength of security measures.
7. IoT and Internet-aware device testing
As the Internet of Things becomes more pervasive, testing the security of IoT devices is essential. This type of testing focuses on devices connected to the internet, assessing vulnerabilities from software, hardware, and network perspectives. It ensures that devices like smart thermostats, security cameras, and other IoT devices are secure against attacks.
Stages of pen testing
Pen testing is a structured process, methodically progressing through distinct stages to uncover and address security vulnerabilities. Each stage, from initial reconnaissance to detailed reporting, plays a crucial role in the overall effectiveness of the test. This meticulous approach ensures a comprehensive evaluation of the system’s security, highlighting both weaknesses and potential attack vectors. Let’s delve into each stage to understand their integral functions in the penetration testing journey.
- Reconnaissance: This initial phase is all about information gathering. Penetration testers collect data on the target organisation to inform their strategy. This can include public information like domain registrations and more covert methods like social engineering. The goal is to map out the attack surface and identify potential vulnerabilities. This stage sets the foundation for the entire testing process, as the quality of information gathered here can significantly influence the effectiveness of subsequent stages.
- Scanning: After reconnaissance, testers move to scanning, using tools to actively probe the target system for vulnerabilities. This involves both static analysis (inspecting application code) and dynamic analysis (examining the application in a running state). The information gleaned from this stage helps in identifying exploitable weaknesses and understanding how the target system responds to various intrusion attempts.
- Vulnerability assessment: This stage builds on the findings from the scanning phase. Testers analyse the identified vulnerabilities, assessing their severity and potential impact on the system. This assessment is crucial in prioritising which vulnerabilities to exploit in the next phase. It requires a deep understanding of the system architecture and potential threat vectors.
- Exploitation: Here, testers attempt to exploit the identified vulnerabilities. This could involve breaching the system through various attack vectors like SQL injections or cross-site scripting. The objective is to determine the extent of damage or unauthorised activities that can be carried out within the compromised system. It's a critical phase where theoretical vulnerabilities turn into tangible security risks.
- Reporting: The final stage involves compiling a detailed report of the penetration test. This report includes the specific vulnerabilities exploited, the sensitive data accessed, and the duration the tester remained undetected in the system. It provides a comprehensive analysis of the system's security posture and offers recommendations for mitigation and improvement. Effective reporting is key to ensuring that the findings of the penetration test are translated into actionable security enhancements.
The next step
Conducting a pentest is more than a security exercise; it's a strategic insight into the fortitude of your organisation's cyber defences. By identifying and understanding your vulnerabilities, you gain invaluable knowledge on where to focus your security enhancements.
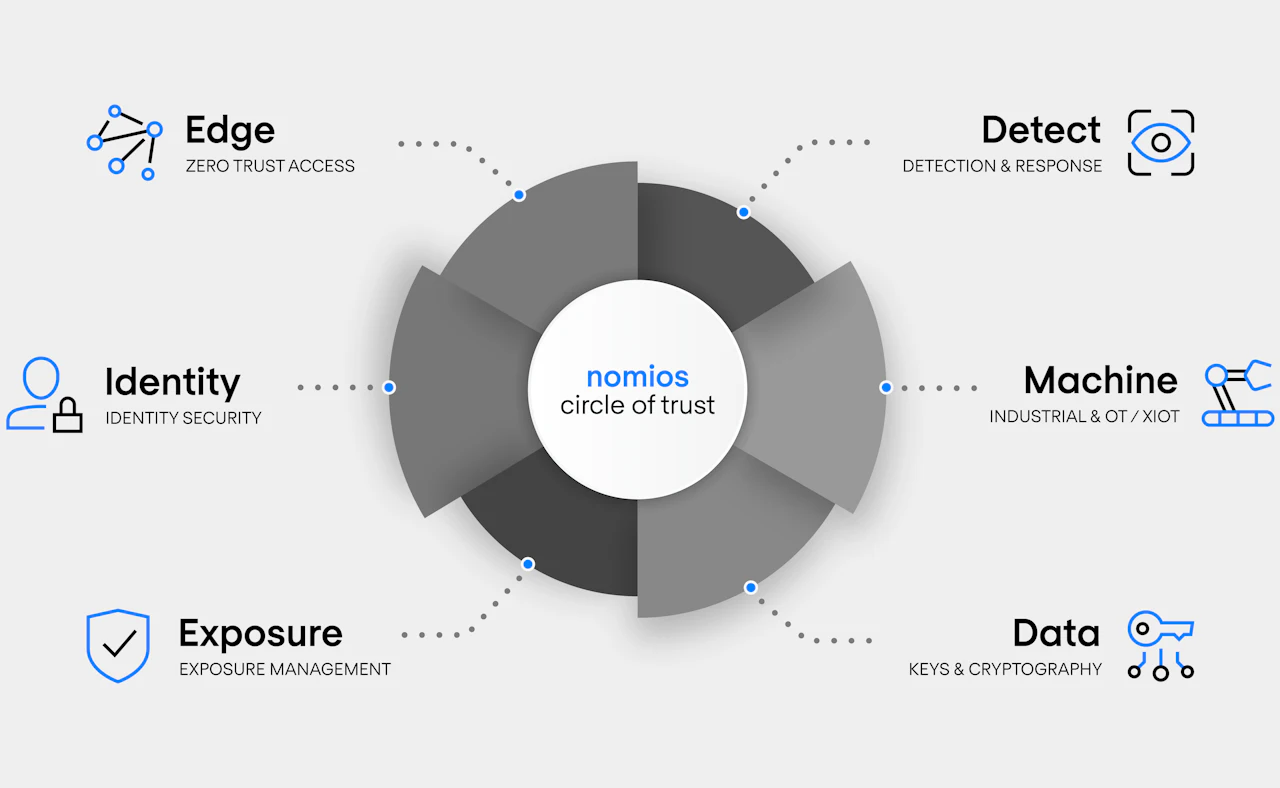
At Nomios, we recognise the significance of this insight. Our expertise in penetration testing and a broad spectrum of security assessments can guide you in fortifying your organisation's digital landscape. Are you curious about how Nomios can tailor a security solution to your specific needs? We invite you to reach out to us for a detailed consultation and discover the path to robust cybersecurity resilience.
Our team is ready for you
Do you want to know more about this topic? Leave a message or your number and we'll call you back. We are looking forward to helping you further.