Cyber defence explained
Cyber defence is the ability to prevent cyberattacks from infecting a network, computer system or device. It involves taking active steps in anticipation of adversarial actions and responding to intrusions, all while preventing them as much as possible.
Defensive strategies help keep you safe by anticipating any future problems before they arise so you can be prepared when it matters most. For example in a situation where you're not aware of a cyberattack on your organisation which could cost you business.
Cyber defence is therefore all about giving organisations the ability to prevent cyberattacks from happening through various cybersecurity solutions, techniques and technologies. A combination of processes and practices to defend a network, its data and nodes prevents unauthorised access or manipulation.
Important techniques in cyber defence
Now that you know what cyber defence is, you’ll understand that it is not just one technique or activity. It is a set of techniques and activities, such as installing and maintaining software and hardware infrastructure that deters hackers. Techniques also include analysing, identifying and patching system vulnerabilities and real-time implementation of solutions aimed at stopping zero-hour attacks. Recovering from a successful cyberattack is also part of cyber defence.
There are several technologies you can set up to prevent cyberattacks against your organisation. Here are a couple of highlights:
SIEM
Security Information and Event Management, (SIEM), is a solution that provides intelligent security analytics regarding your most critical threats. SIEM solutions can pull data from disparate systems or use a separate log management platform to create a single pane of glass visibility. This facilitates efficient cross-team collaboration and continuous real-time monitoring and correlation across the breadth and depth of the enterprise security and network domains. It also allows for continuous compliance reporting.
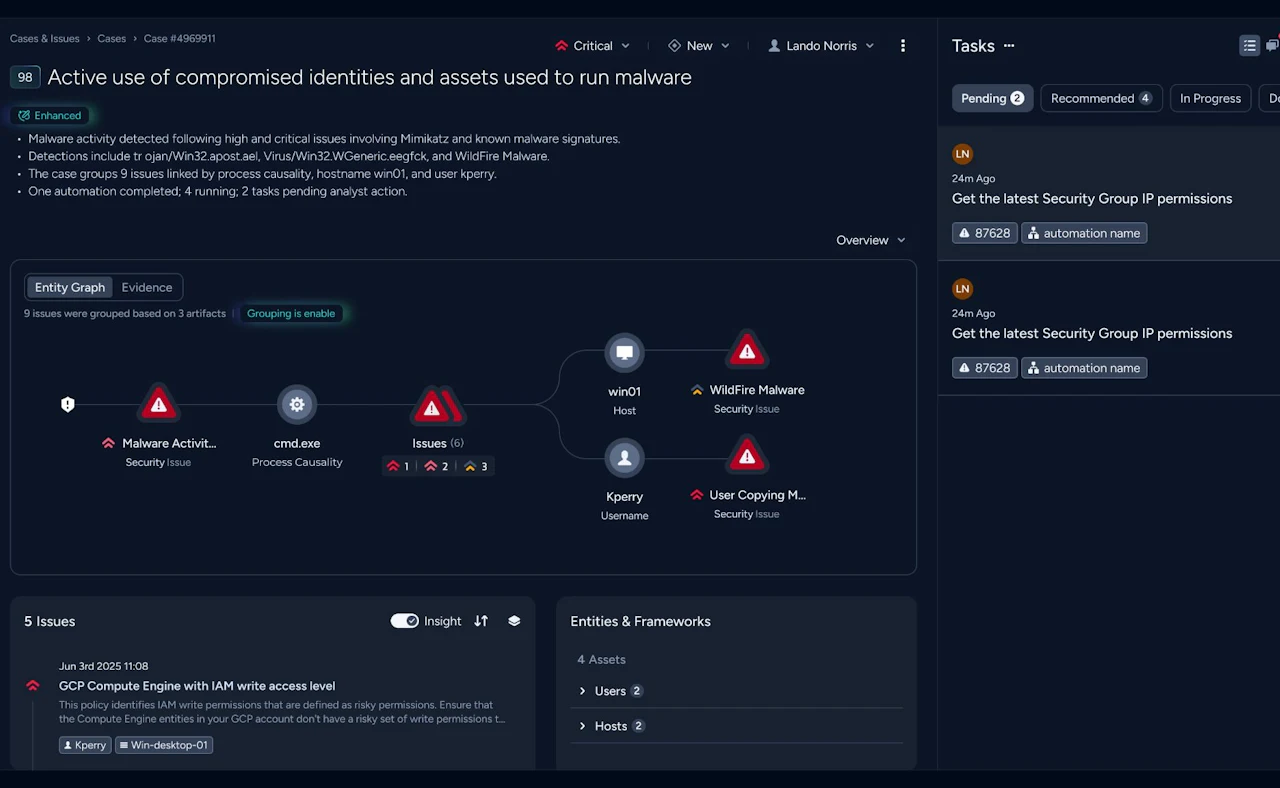
XDR
Most approaches, such as SIEM, are layered approaches. This is effective in detecting and responding to cyber threats but it has its limitations on its own.
Extended Detection and Response (XDR) takes a different approach. Instead of a purely reactive approach to security, XDR enables an organisation to proactively protect itself against cyber threats by providing unified visibility across multiple attack vectors.
SOAR
Threat detection is only half of the security equation. Organisations also need smart incident response to the growing volume of alerts, multiple tools and staff shortages. Security Orchestration, Automation and Response (SOAR) accelerate incident response with automation, process standardisation and integration with your existing security tools.
Mature organizations are adopting SOAR platforms and working with consulting and managed services to improve their security operations centres. This proactive approach to security threats delivers the critical elements of a successful zero-trust strategy.
A complete approach: managed security services
You do not have to figure all of this out by yourself. For a superior quality setup of cyber defence, it takes a lot of knowledge and manpower in-house to keep your security up to date. By working together with external experts on your cybersecurity, you save a lot of time and simultaneously gain knowledge.
You can do this with managed security services. This will improve your security posture while reducing the burden on your IT team with an experienced partner.
With, for example, Managed Detection and Response (MDR) you’ll have 24x7 treat monitoring and protection, a dedicated team of security experts, security posture overview and reporting and state-of-the-art security technology as described above. And you’ll improve ROI and save time because you don’t need to hire your own security staff or do expensive investments in the latest technology.
Managed SOC, or SOC as a Service, offers organisations external cybersecurity experts who monitor your cloud environment, devices, logs, and network for threats. Read more
Security professionals - red team vs blue team
To test if your infrastructure is safe from attackers, you can make use of the expertise of red and blue teams. Red teams are offensive security professionals (ethical hackers) who are experts in attacking your systems and breaking into defences. Blue teams are defensive security professionals. They are responsible for maintaining internal network defences against cyber threats and attacks.
To test your cyber defence, the red team will use all the available techniques to find weaknesses in people, processes, and technology to gain unauthorised access to your assets. The blue team’s task is to protect your organisation’s important assets against any kind of threat. In this case the red team’s threats.
Related solutions & services
Take a look at our cyber defence solutions and services. Our strength lies in our flexibility and focus on developing tailor-made solutions.
Our team is ready for you
Do you want to know more about this topic? Leave a message or your number and we'll call you back. We are looking forward to helping you further.