Tufin Orca provides cloud-based, security automation for container and microservice environments. From vulnerability scanning and compliance validation during every CI/CD cycle to identifying risks at runtime and taking policy-based action, Tufin Orca shields applications from constantly evolving threats.
How Tufin Orca fits in the Tufin portfolio
A continuum from the macro to the micro
Tufin is the leading provider of security policy orchestration across complex, physical and hybrid cloud environments. Orca extends the Tufin platform to deliver trusted security automation to microservices.
Why Tufin Orca?
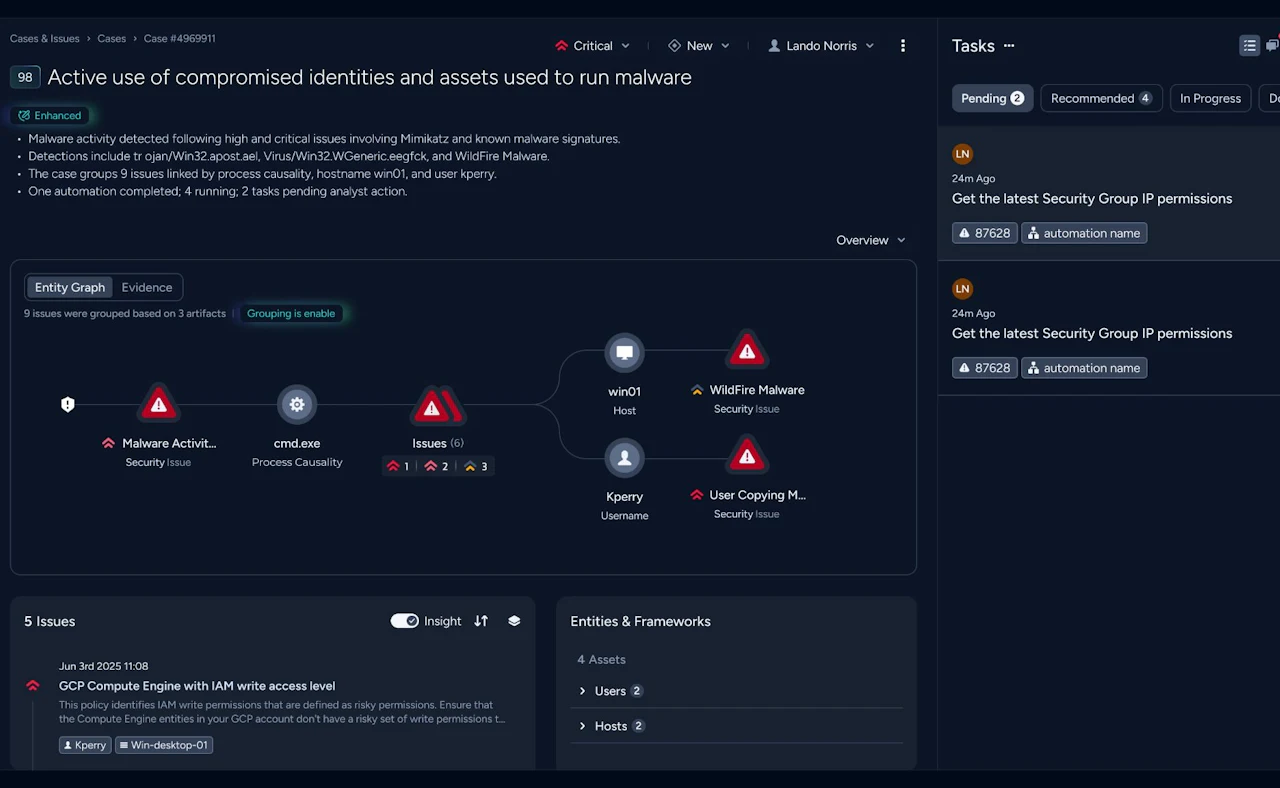
- View all services, containers, connections and policies, and make real-time configuration changes
- Detect and resolve policy validation errors during development and enforce compliance at runtime
- Identify and protect against container vulnerabilities in both development and deployment stages
- Protect network traffic and limit breach expansion with automated microsegmentation and encryption
- Automate risk monitoring and anomaly detection, as Orca takes policy-based action to shield applications
- Integrate third party notification and security services for custom protection using Orca’s open API
Visibility and control
Continuous compliance
Vulnerability scanning
Minimise attack surface
Adaptive security
Customisable services
Ready to talk?
Are you looking for pricing details, technical information, support or a custom quote? Our team of experts in Dortmund is ready to assist you.