NetFlow is an enabler of modern network management and security. It is the most widely used standard for network traffic monitoring providing network administrators, security engineers and operations managers with deep knowledge about their IT environment. NetFlow brings completely new effectiveness when IT professionals perform troubleshooting, capacity planning, performance diagnostics and many other tasks.
The next-generation network performance and security management
For years, regular monitoring of a network was performed by the SNMP protocol that delivers an overview of the IT infrastructure; giving network administrators information about the availability of its components. Today, when the availability and proper working of a company's network is crucial for its existence, much more information and sophisticated methods are needed. To get this information Cisco has created NetFlow, a standard for collecting network traffic statistics from routers, switches or specialised network probes.
NetFlow provides information from layer 3 and layer 4 which means IP addresses, ports, protocol, timestamps, number of bytes, packets, flags and several other technical details. It could be easily imagined as a list of phone calls. We know who communicates with whom, when, how long, how often etc.; but we do not know what the subject of the conversation was. By collecting, storing and analysing this aggregated information, network administrators, security engineers or operations managers can run proceed with several tasks.
Collecting Netflow. How does it work?
NetFlow is the most widely used standard for flow data statistics in network communication. In the language of a data network environment, one flow represents a network communication with the same source IP address, source port, L4 protocol, destination IP address and destination port. NetFlow is available in different versions that significantly vary so that understanding the NetFlow version is important when choosing the right solutions for particular needs:
- NetFlow v5 – the most common version available on various routers and active network components. However, this version does not meet current needs. NetFlow v5 does not support IPv6 traffic, MAC addresses, VLANs or other extension fields.
- NetFlow v9 – template-based standard described in RFC 3954. It supports IPv6 as well as the fields missing in NetFlow v5.
- NetFlow v10 aka IPFIX – standardised by IETF, extended version of NetFlow v9 that supports variable length fields (e.g. HTTP hostname or HTTP URL) as well as Enterprise-defined fields.
Currently, the most used versions are NetFlow v5 (fixed format) and NetFlow v9 (template-based, flexible). Another commonly used protocol is called IPFIX, also known as NetFlow v10. Internet Protocol Flow Information Export (IPFIX) was created by the IETF working group from the need for a common, universal standard of export for IP flow information. The IPFIX standard defines how IP flow information is formatted and transferred from an exporter to a collector. Previously many data network operators relied on the proprietary Cisco NetFlow standard for traffic flow information export. The IPFIX is a much more flexible successor of the NetFlow format and allows us to extend flow data with more information about network traffic.
Understanding NetFlow principle animation
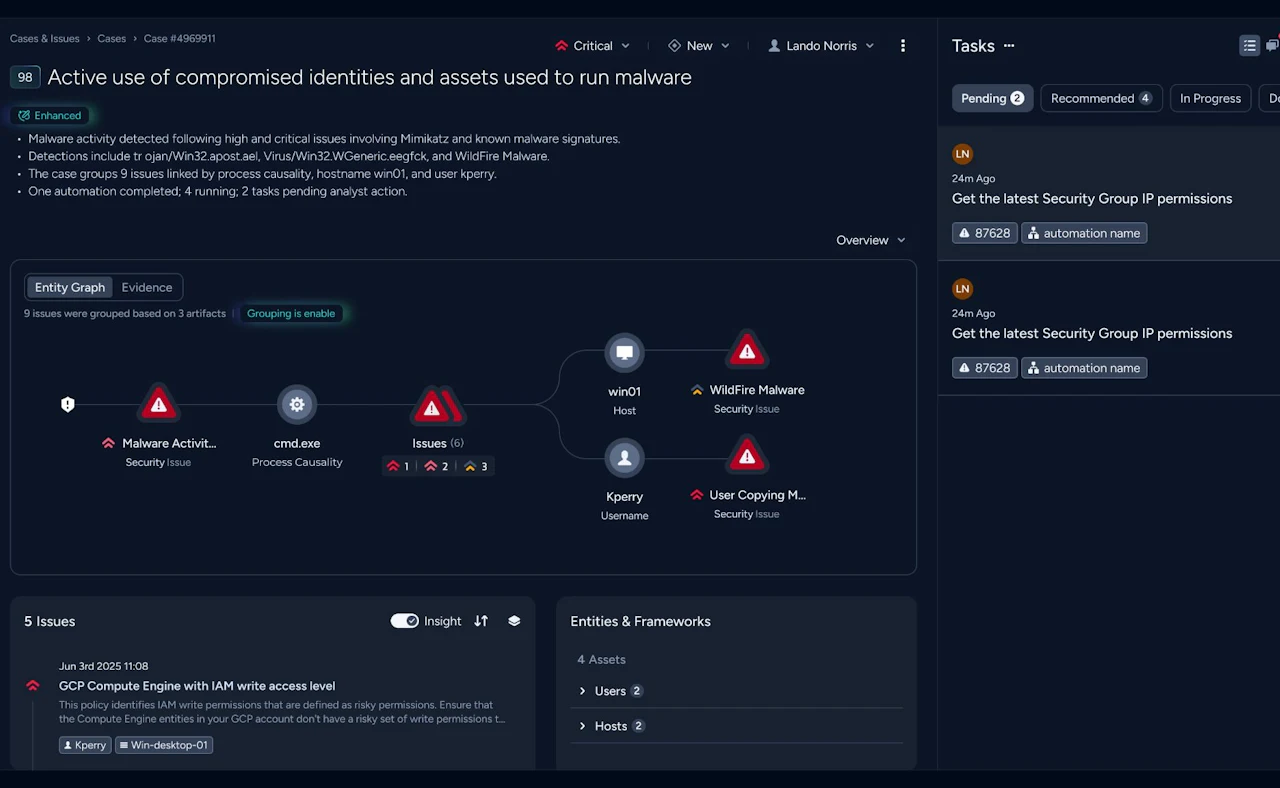
The principle of NetFlow is described in the video above. When a request from a client to the server is sent (green envelope), the active device with NetFlow export capability looks into the packet header and creates a flow record. The flow record contains information about the source & destination IP addresses and ports, protocol number, number of bytes and packets and all other information from layer 3 and 4. Individual data network communications are identified by five attributes: source & destination IP addresses, ports and protocol number. So when the server responds to the client IP addresses and ports in the packet header are reversed and another flow record is created – NetFlow is one-way traffic technology. The subsequent packets with the same attributes update the previously created flow records (e.g.: number of bytes, duration of communication). When the communication is over, flow records are sent to the collector, where data is ready to be stored and analysed for different reasons.
Key features
Know the network at any time and any point
Troubleshoot the network failures fast and precisely
Monitor network traffic in real-time
Introduce intelligent traffic and financial reporting
Secure the network against internal and external threats
Plan and monitor QoS policy in detail
Ready to talk?
Are you looking for pricing details, technical information, support or a custom quote? Our team of experts in Dortmund is ready to assist you.