On July 6th, 2022, for the first time, the Directors of the British MI5 and the American FBI spoke jointly to leaders of the business and academic world. The objective of their speech was straightforward: to warn about the threat posed by the Chinese Communist Party and its aggressiveness in industrial espionage and technology theft. Undeniably, China is not the only actor involved in this activity and the opposite accusations have been made against the United States. While industrial espionage is far from being a recent phenomenon, it has taken another form in the digital age: cyber industrial espionage.
Cases of cyber-attacks motivated by data theft are frequent and come from all continents, and it is reasonable to assume that the majority of them are neither discovered nor brought to the attention of the public. The perpetrators of these actions are difficult to identify, particularly because of the porosity of state and private actors with overlapping interests. The majority of cyber-espionage activities are carried out by APTs (Advanced Persistent Threats), sometimes supported by a nation-state, characterised by the sophistication of their attacks and the durability of their access in a compromised network.
The objective of the attacker is to gain a competitive advantage, to make a profit by selling the information obtained, or to damage the reputation of a competitor. All companies are concerned by the risk of cyber-espionage, although there is a strong prevalence of the threat in strategic sectors such as research centres or high-tech industries, particularly in the military field. Protection against industrial cyber-espionage is therefore an economic and strategic issue.
According to a 2017 report from the US Intellectual Property Commission, commercial data theft has cost the US between $180 billion and $540 billion.
How to protect yourself and detect indicators of compromise in an industrial espionage attempt?
1st step: Identify the risks
Human risk
The human factor is often the initial vector in a cyber-attack. Indeed, intentionally or not, a human flaw is often at the origin of the compromise. Depending on the sensitivity of the sector, clearances may be issued to access classified documents. A security investigation is carried out on the individual and his or her entourage in order to determine the levers that could be exploited and lead to the disclosure of classified information.
Despite this precaution, an employee with access to information of interest may be targeted by a business competitor or foreign intelligence service. This approach can be conducted entirely virtually, without any real-world interaction. By using social engineering – via a simple LinkedIn message, or through a BEC attack impersonating a manager who demands to open a rogue attachment, for example – it is possible for a cyber-spy to gain access to a network.
According to an ECIPE estimate, [...] by 2025, commercial data theft will result in a financial loss equivalent to 1 million jobs in Europe.
Hardware and software risk
In the context of cyber-espionage, potential hardware and software vulnerabilities must be addressed quickly. The team responsible for information systems security must constantly monitor published CVEs and ensure that its IT stock is properly updated. In addition, network mapping must allow to identify particularly sensitive devices (because they contain classified information, or because they control some or all of the network’s machines, etc.) and to identify any points of vulnerability. The use of a tool, such as the TEHTRIS EDR, can help in this task because it allows to launch compliance audits to verify the state of a station by comparing it to a repository.
In the case of USB flash drive (especially on an air-gap machine, i.e. one that is physically isolated from any computer network to limit remote hacking attempts), the use of a sheep-dip is essential to ensure that malware will not be introduced through this means. Indeed, not all intrusions are done remotely and a compromised USB flash drive can contain a spyware . The purpose of the white stations is to analyse and – if necessary – “clean” USB devices before inserting them into a company machine.
2nd step: Prevent
Once the risks have been identified, the next step is to anticipate the threats. On the one hand, it is essential to raise awareness and train company staff on an ongoing basis. Regular exercises simulating a cyber-attack, by running a fake phishing campaign for example, aim to make employees develop better reflexes. In addition, it is important not to neglect the organisation of regular awareness campaigns about the knowledge and handling of the different data classifications within the organisation, as well as the limitation of access to these classified data to people who need to know them in order to limit the risk of spreading sensitive information.
On the other hand, the use of cybersecurity software protection is essential to protect your assets from cyber threats. The team in charge of information systems security can carry out the following actions as part of prevention:
- Verify that multi-factor authentication (MFA) is enabled. While MFA is not foolproof, the purpose of this security approach is to make it more difficult for an attacker to get in.
- Ensure the presence of EDR (Endpoint Detection Response) on all the company’s endpoints in order to, on the one hand, obtain sufficient visibility on the network and, on the other hand, benefit from a response capacity in the event of an attack detection. The goal is to have no blind spots on the endpoints.
- Set-up the SIEM to include high-value sources. Indeed, what enters and leaves the internal network must be logged. For example, VPN connection logs must be saved – for later analysis in case of an incident, or to raise alerts in case of unusual events. Studying logs in a SIEM tool will allow correlating and contextualising events to determine if they are questionable: an attempt to connect from an IP in an abnormal geographical area, the creation of a new user with administrator rights on the machine, the deletion of security logs…
- Configure a network protection with the DNS Firewall which is placed on top of a traditional firewall and will be able to prevent a spyware from establishing the connection to its command and control (C2) server to exfiltrate data.
- Deploy a honeypot network to detect scans and attempts by attackers to exploit vulnerabilities. This information is invaluable for early detection of threats and for focusing attention on devices and applications that are targeted by hackers.
3rd step: Detect and hinder
Attacks aimed at exfiltrating sensitive data are characterised by their discretion. The cyber spy wants to avoid detection in order to stay on the targeted network as long as possible. However, cybersecurity tools, such as TEHTRIS solutions, can help detect and disrupt a cyber espionage operation.
TEHTRIS EDR provides automatic attack alerting and remediation, including TEHTRIS Cyber Threat Intelligence, which will identify a binary with suspicious behaviour. By enabling automatic remediation based on thresholds set by the analyst, no human action is required to protect against the threat. In addition, it is possible to configure an alert escalation on more subtle and discrete actions, such as Living off the land (attacks using tools already available on the machine). For example, an attacker can use a procdump (tool from the Sysinternals suite) instead of using malware to perform malicious actions. This tool can be used by administrators in a legitimate way and is already often on the servers. TEHTRIS EDR gives you a complete view of what is happening on your network, at any time, and allows you to make better judgements on what actions to take on “grey” tools (administration tools that can be hijacked for malicious purposes).
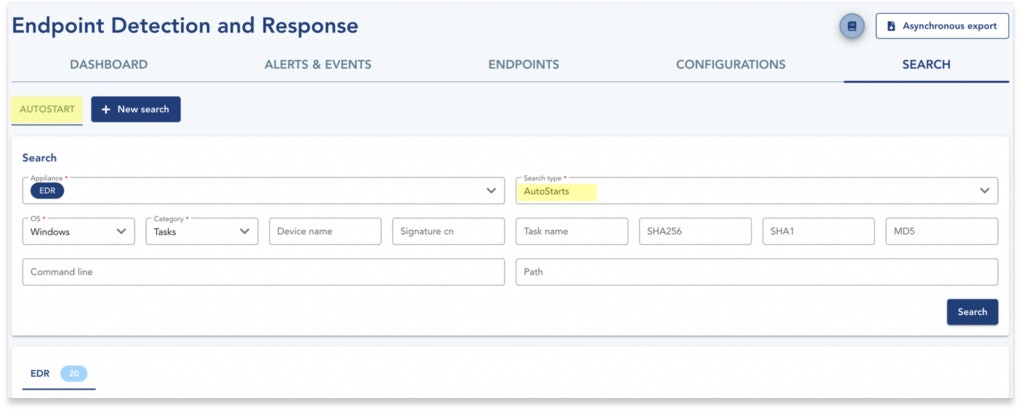
The Autostart module of the TEHTRIS EDR is an asset while monitoring the park because it allows to keep an eye on the processes launched at the start of the machine (by raising an alert, or by quarantining the binary). Unlike the duration of a ransomware attack, which is counted in hours or days, in the context of industrial cyber-espionage, the attacker seeks persistence to maintain itself for several months or even years. If a persistence trace is discovered on the park, the Autostart module allows to investigate on a retroactive period to identify the beginning of the compromise.
The combination of TEHTRIS tools provides enhanced protection for your IT assets against cyber espionage. The XDR platform that unifies these tools eliminates the blind spots on your network where spies hide.
Although it is difficult to assess cyber-espionage activities because they are obviously discreet and sensitive, this threat is real and has serious consequences for industries whose business depends on the protection of these patents and R&D progresses. Without neglecting the human factor, choosing robust cybersecurity tools is essential for protection. A combination of complementary tools is vital to obtain the highest possible visibility on the security of an industry’s information system. The use of TEHTRIS XDR, a unified solution integrating different technologies (endpoint protection, DNS request analysis, log collection via a SIEM…) allows the analyst to have a global view of the IT assets that will help him anticipate, detect and remedy cyber-espionage attempts.
Cybersecurity: The upside and downside of AI
Get your copy of this whitepaper, to learn more about cybersecurity, XDR, EDR and how AI drives security. Or get in touch with us directly if you find this topic of interest.
Continue reading about TEHTRIS

XDR Cybersecurity
Best XDR solutions to check out
Almost 70% of breaches start from endpoints, highlighting the need for robust security measures, such as XDR.

Inès Khabkhabi

XDR Cybersecurity
Best XDR solutions to check out
Almost 70% of breaches start from endpoints, highlighting the need for robust security measures, such as XDR.

Inès Khabkhabi


MDR XDR
Strengthening cybersecurity in the public sector: how MDR and XDR help
If you are active in the public sector, cybersecurity and data safety are extremely important. Find out how MDR and XDR help you strengthen and solidify your security frameworks.

Inès Khabkhabi