Artificial Intelligence
Project Glasswing: when AI finds vulnerabilities that lay hidden for thirty years
Anthropic has launched Project Glasswing together with a coalition of twelve leading technology and security companies.

Richard Landman

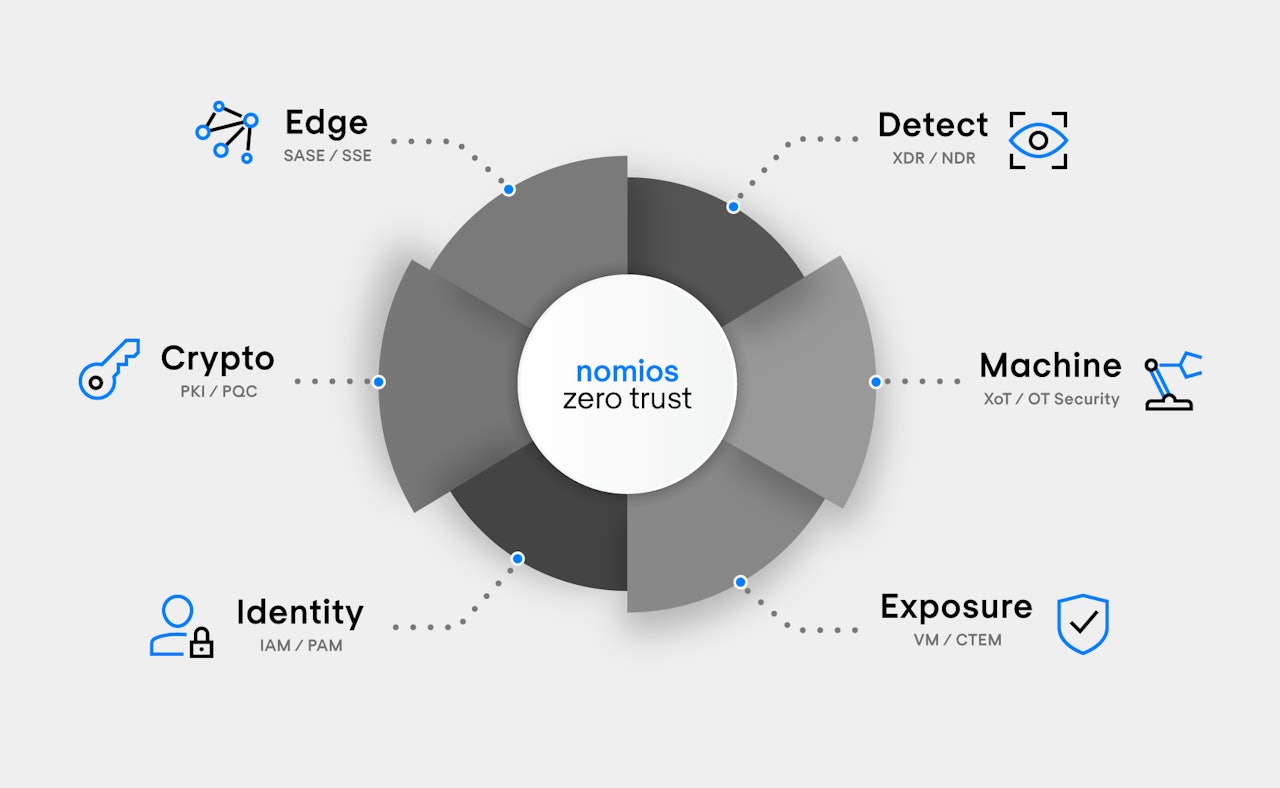
SIEM MDR
Cortex XDR as SIEM light: powerful detection and compliance without the complexity
Many organisations face the same dilemma: they know they need better visibility into what is happening across their environment, but a full SIEM platform feels like a significant undertaking — expensive, complex to manage, and heavy to implement.

Richard Landman


Digital Sovereignty
Digital Sovereignty That Works in Practice: Local Control, Global Resilience
Zscaler introduces the expansion of its digital sovereignty capabilities.

Richard Landman

Zero-Trust Identity management
Why identity is the engine of zero trust
Identity is the engine of zero trust: learn how IAM, PAM and IGA enable continuous verification, reduce risk from privileged access, and strengthen identity hygiene across cloud and hybrid environments.

Mostafa Kamel

NIS2
A practical NIS2 guide for network managers and IT directors
For network managers and IT directors, NIS2 does not significantly alter what is technically required, but it substantially raises the bar on what must be demonstrable.

Richard Landman

par
Change of leadership at Nomios Germany: Focus on security and connectivity

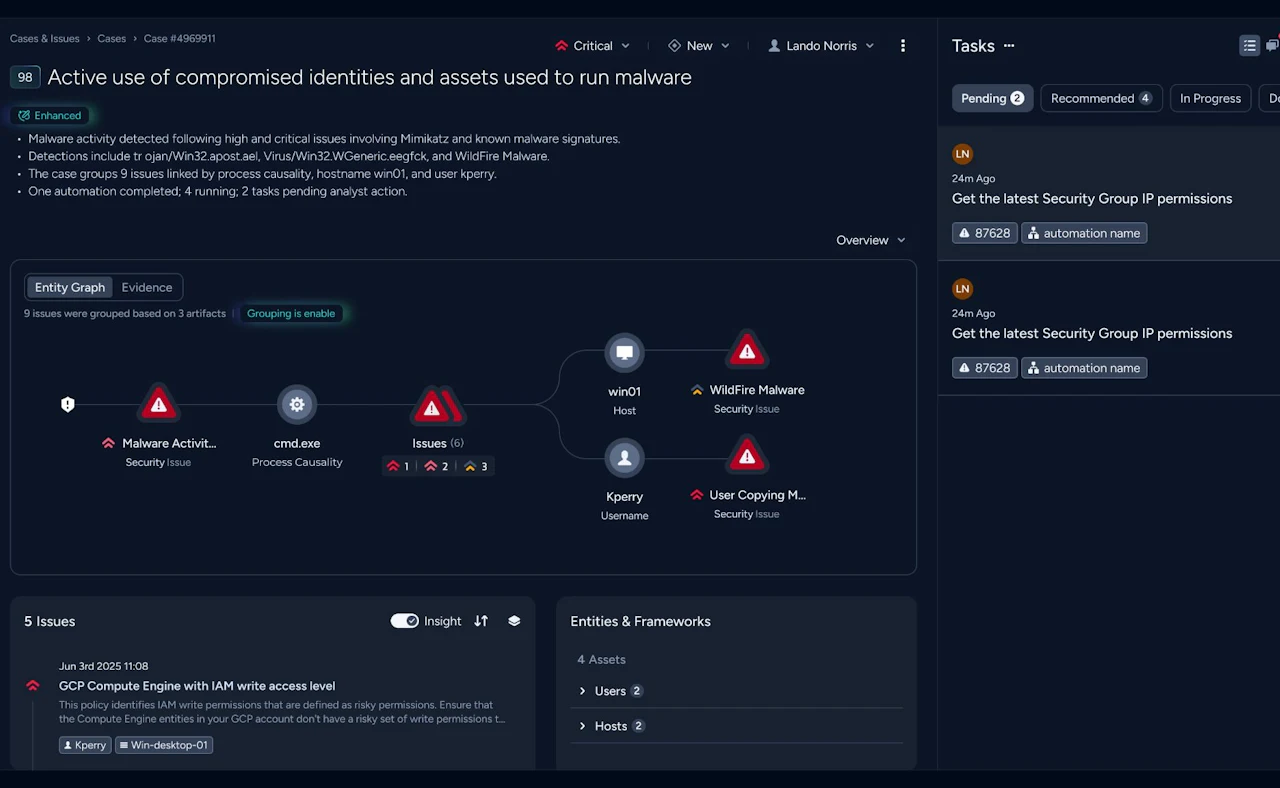
OT security
Passion as the quiet driver of OT security
Cybersecurity in industrial environments is rarely visible or dramatic. Yet a large part of the German economy depends on it.

Richard Landman

PKI
Why PKI is becoming a strategic pillar of modern cybersecurity
It often starts with something small. An application that suddenly becomes unavailable. An API integration that fails without a clear reason.

Richard Landman

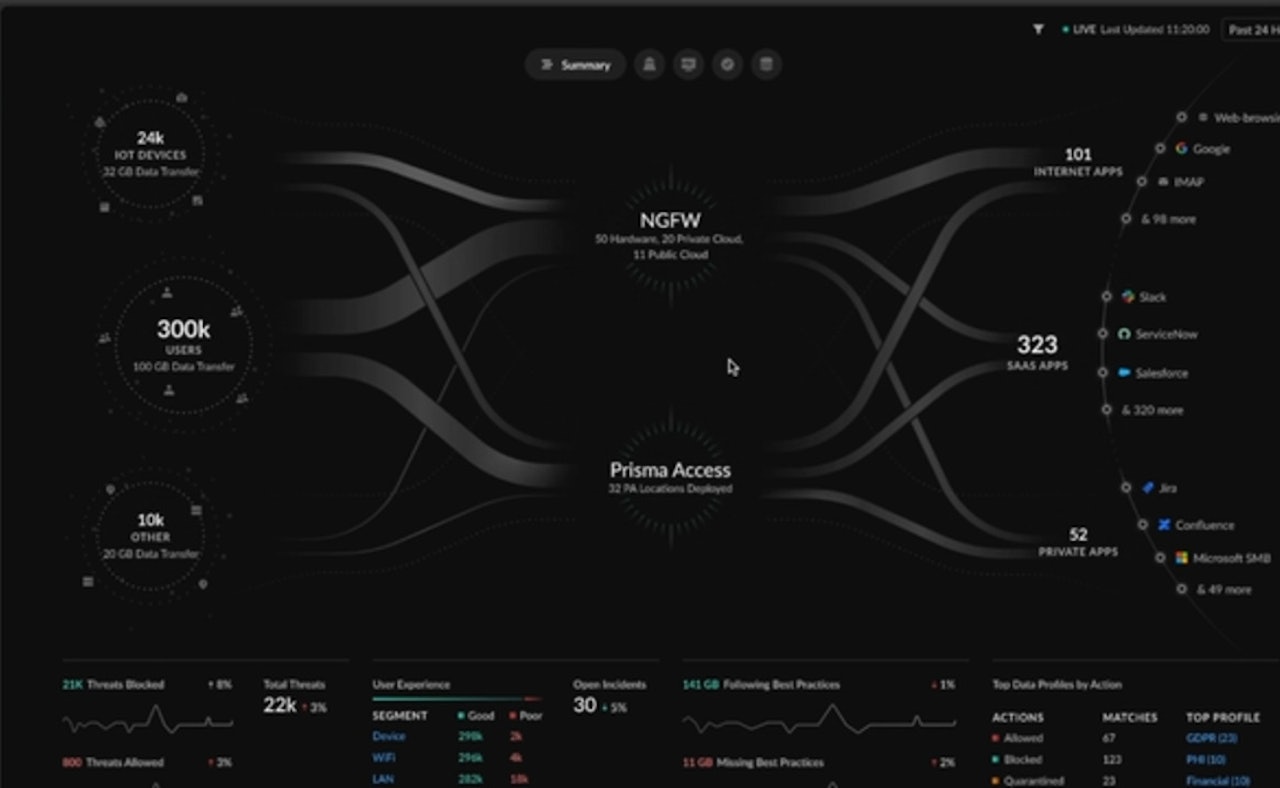
NGFW Firewall
Top 5 NGFW solutions for 2026
Explore the state of NGFW in 2026. Learn how leading next-generation firewall platforms support zero trust, hybrid cloud security, and risk reduction for modern enterprises.

Enrico Bottos


Network security
Securing sensitive traffic in research networks
How research and education networks secure sensitive traffic with line-rate encryption and real-time DDoS mitigation, without impacting performance or reliability.

Michel Geensen
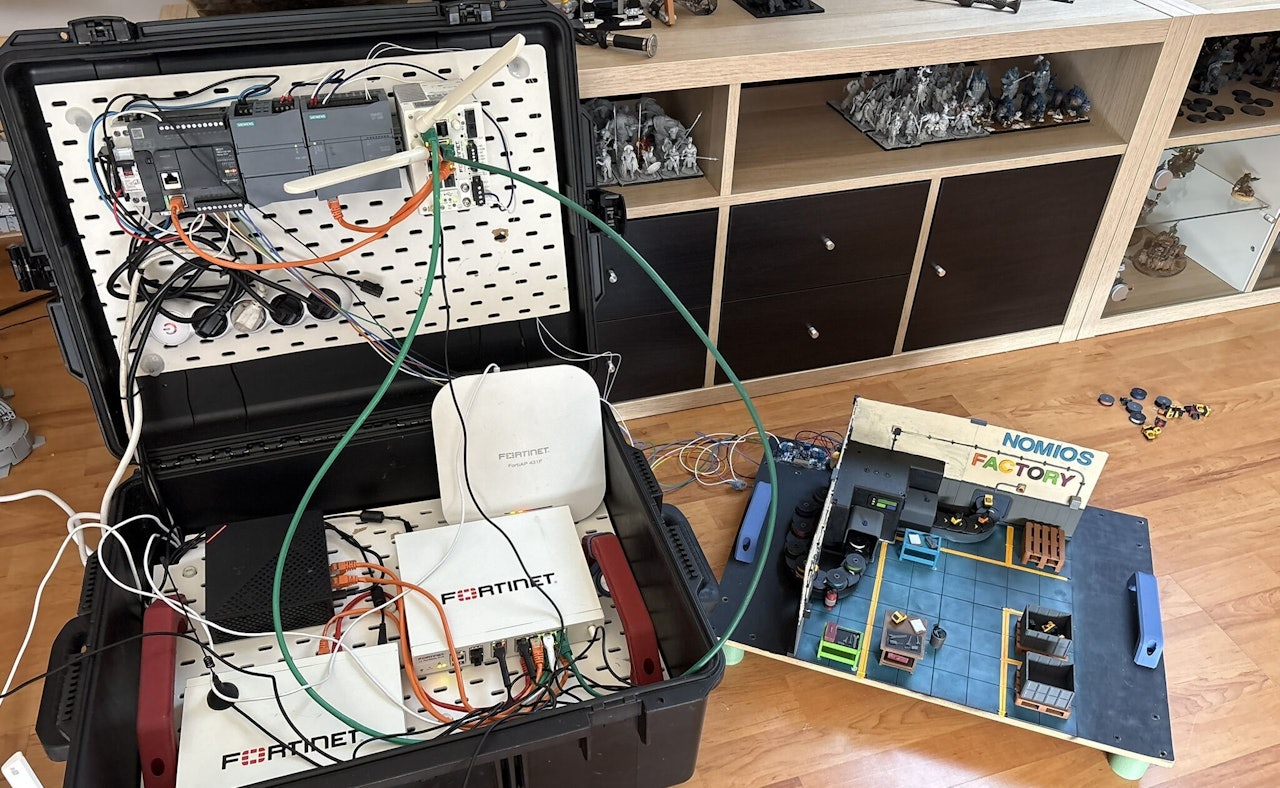
Portfolio
Nomios Zero Trust: one cybersecurity portfolio, six domains
Nomios is introducing a refreshed cybersecurity portfolio that doesn’t start with individual products, but with an architecture.

Richard Landman

Cybersecurity
Cybersecurity in 2026: Top 10 trends and challenges
Cybersecurity trends for 2026 cover digital sovereignty, quantum security, SSE and identity security, detection, compliance, and managing trust across complex environments.

Richard Landman

SSE IAM SASE
Single vendor SASE? It’s all about strategic partnerships
Across the market we see a clear shift towards single vendor SASE. Organisations want to simplify their IT landscape, reduce operational overhead, and gain better visibility across network and security.

Richard Landman

Cybersecurity
Top cybersecurity companies to watch in 2026
We selected the top cybersecurity companies to watch in 2026, who have successfully differentiated themselves from other players in the market.

Mohamed El Haddouchi

Palo Alto Networks Whitepaper
Rethinking the SOC for today’s threat landscape
Explore why organisations are moving away from traditional MSSP and SIEM models. The whitepaper shows how a Cortex-based SOC delivers clarity, speed, and better security outcomes.

Palo Alto Networks
Why now is the time to migrate from Panorama to Strata Cloud Manager
With Strata Cloud Manager, Palo Alto Networks has introduced a cloud-native platform that brings management, automation, and visibility together. And now is the perfect time to make the move.

Richard Landman

Network automation
Building trust in automation: why spreadsheets hold networks back
Discover why spreadsheets limit automation and how a trusted source of truth empowers modern network operations.

Adam Kirchberger

Network infrastructure
Why Wi-Fi site surveys matter more than ever
Reliable Wi-Fi has become essential in the modern workplace, not just a convenience. Poor coverage or unstable networks can disrupt productivity, collaboration, and critical services.

Giulio Quartero
Sign up for our newsletter
Get the latest security news, insights and market trends delivered to your inbox.