Ivanti Neurons for Secure Access
Ivanti® Neurons for Secure Access helps customers modernise their VPN deployments by centralising Ivanti Connect Secure (VPN) and Ivanti Neurons for Zero Trust Access management. This new cloud-based management approach provides greater control and insights into network and access status than ever before.
Deliver secure access foundation everywhere
Ubiquitous management of policies and environments to enable access to applications and networks.
- Leverages a cloud-based management approach.
- Supports a hybrid IT model (on-prem, cloud, and edge).
- Works across legacy or new Ivanti CS (VPN) and Ivanti Neurons for ZTA environments.
Secure Access delivers one approach.
Design and customise your journey to SASE*
No vendor delivers both the ability to modernise a VPN deployment and transform into a Zero Trust architecture.
- Easily integrates existing and configured VPN.
- Evolve to Zero Trust (easiest path to ZT).
- Take advantage of Ivanti’s key differentiator – the Software-Defined Perimeter (SDP) architecture.
Secure access manages with ZERO configuration change required.
Streamline management
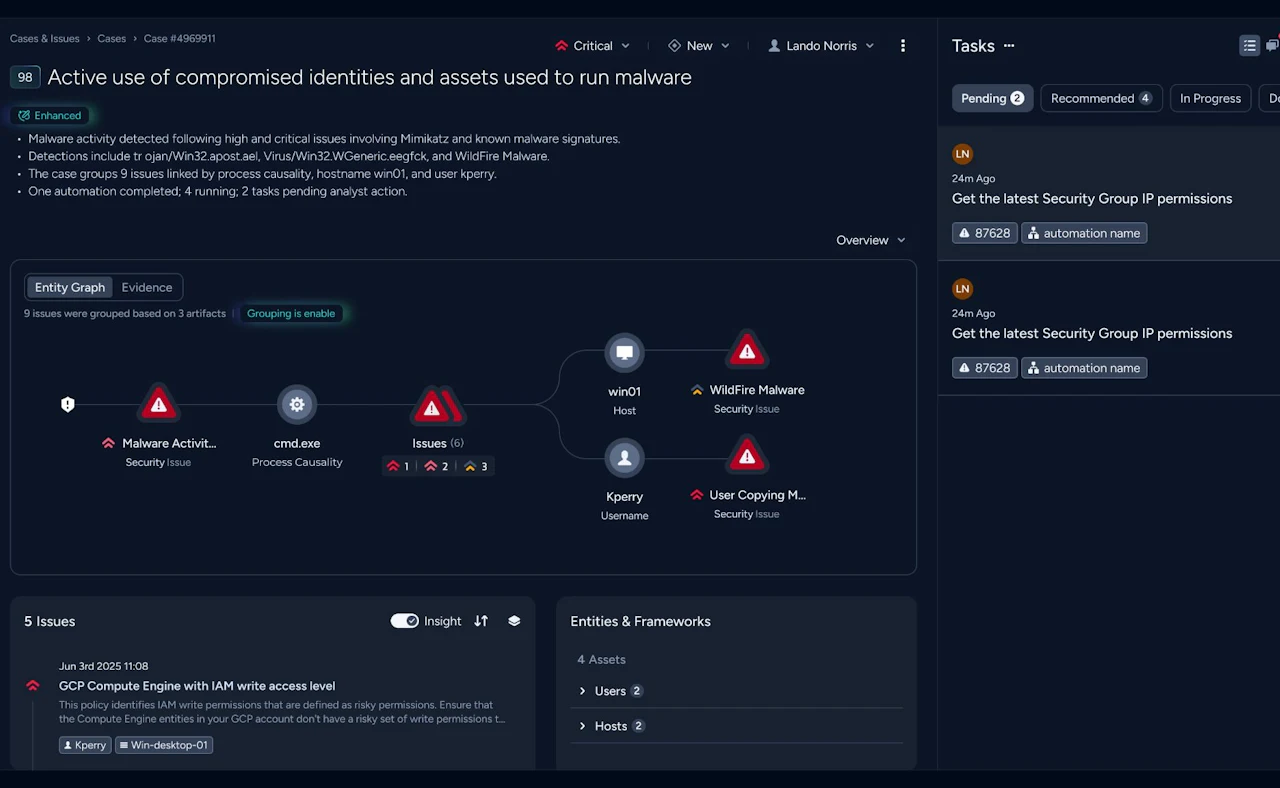
Automation and enhanced management = enhanced security and time savings for SecOps.
- Learn from user behavior to adapt security response initially and “on the fly”.
- Utilise a single pane of glass view for all gateways, users, devices, and activities.
- End management overhead.
Secure Access produces 5x-20x time savings in management overhead**.
(*Secure Access Service Edge).
(**Compared to previous VPN management).
Why Ivanti for secure access?
Ivanti Neurons for secure access helps customers modernise their VPN deployments by centralising Ivanti Connect Secure (VPN) and Ivanti Neurons for Zero Trust Access management. This new cloud-based management approach gives greater control and insights into network and access status than ever before.
- A single, cloud-based interface for managing Connect Secure Gateways and/or Zero Trust Access Gateways in all aspects. Most vendors have separate clients for VPN, software gateways and access. nSA allows for management of existing and next-gen VPN gateways plus can co-exist with 3rd party VPN offerings.
- The core management construct is a cloud-based offer that allows for simplified setup and management. This approach also allows for management of gateways and assets regardless of location. Cloud, on-prem, edge – no problem.
- Supports gateway configurations. Configuration groups for multi-node config management.
- Leverages analytical data to reduce security risks, detect anomalies, optimise user experience and adapt to mobile workforces.
- Enables centralised upgrades, downgrade, and restarts.
- Clean APIs to facilitate easy application integration (IDP, SIEM, UEM, vulnerability assessment, and endpoint protection).
Single foundation
Hybrid cloud configuration support
Configuration management
User behavior analytics
Gateway lifecycle management
Extensibility with 3rd party integration
Zero Trust Access
- Increase security for remote users.
- Reduce privileged access to apps, environments, and data.
- Gain insight into visibility and analytics and user behavior.
- Continual verification and enforcement of apps, users, and devices.
- Granular policies help enforce HR access policies around movers, joiners, and leavers.
Ready to talk?
Are you looking for pricing details, technical information, support or a custom quote? Our team of experts in Dortmund is ready to assist you.